How you can leverage both ABAC and Delta Sharing across governance boundaries
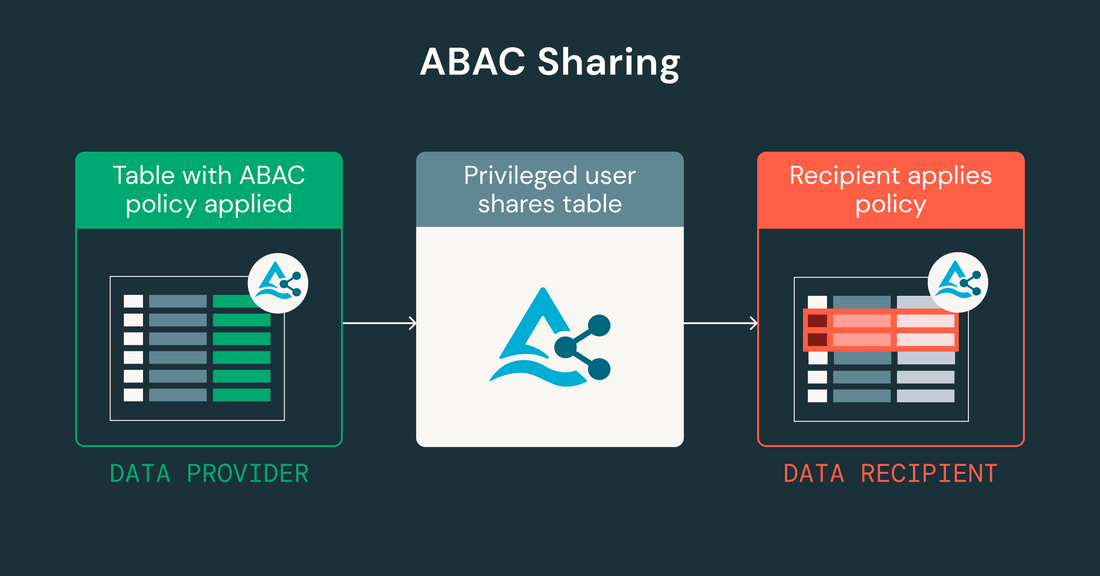
ABAC-governed tables can now be Delta Shared across organizational boundaries. The provider and the recipient each separately apply their own ABAC policies that conform to their own internal governance.
by Tia Chang, Harish Gaur and Yin Ouyang
- Share tables governed by attribute-based access control across catalogs and schemas.
- Recipients can apply their own ABAC-based row filtering and column masking policies on Delta Shared tables.
- Providers can have a single table for both internal usage - governed by local ABAC policies - and for external sharing.
Organizations need to share data quickly. But keeping that data secure at scale is often difficult. Delta Sharing now supports Attribute-Based Access Control (ABAC), enabling you to share tables secured with ABAC policies that use governed tags. Providers can now share the entire tables directly without creating separate copies, and recipients can apply their own local ABAC policies with the guarantee of correct query-time enforcement.
Why ABAC Sharing Matters
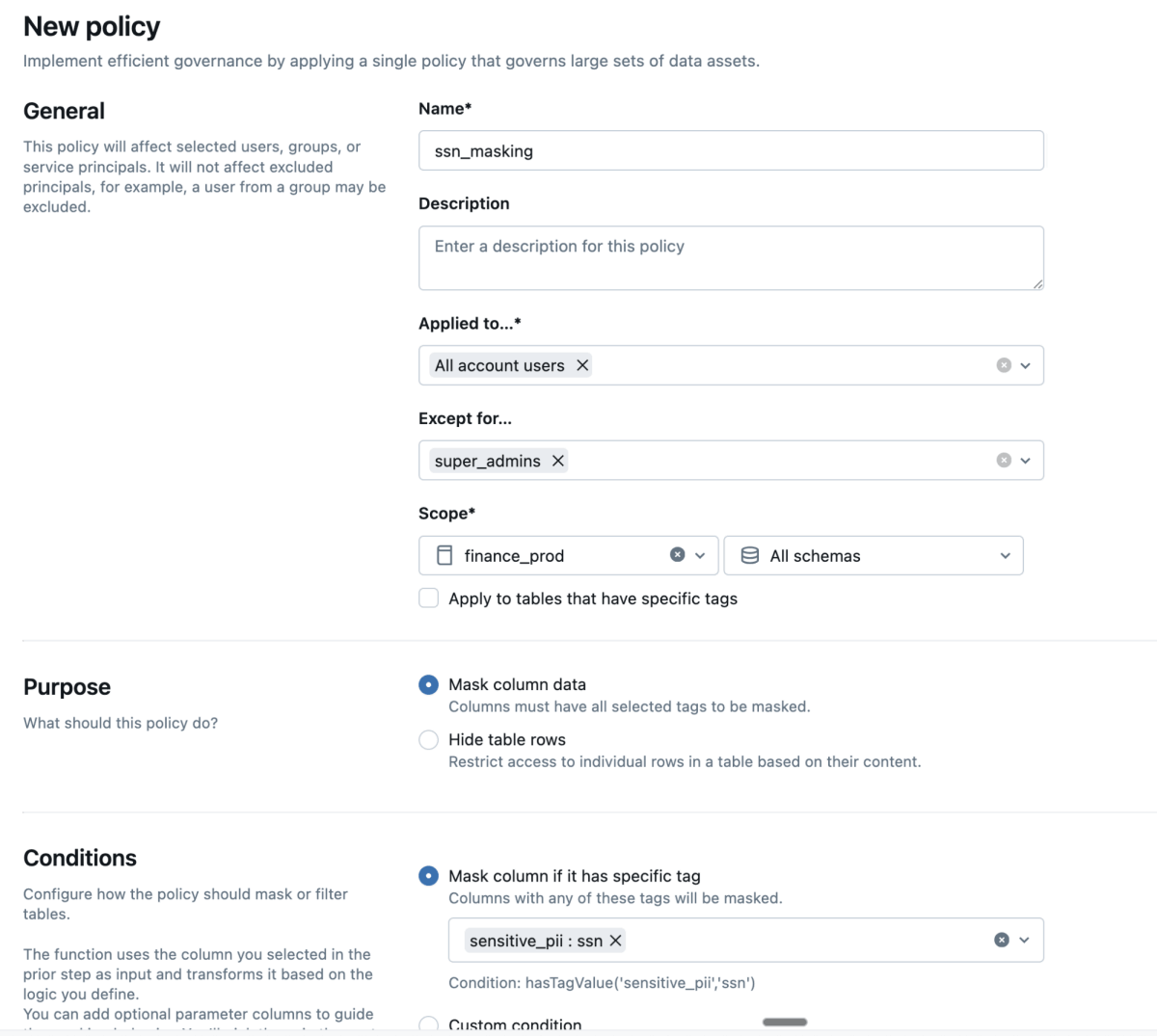
ABAC is an access control model based on policies that determine access by evaluating attributes of resources, such as their type or tags applied to them. For example, ABAC can mask any column with a 'sensitive' tag to '*****', or restrict access to records in tables with a 'sales' tag so that users only see the rows they are authorized to view.
Read how ABAC works in Unity Catalog
Data providers can now share ABAC-governed tables directly. The provider's ABAC policies are enforced on the provider's side, controlling what data is accessible to internal users. To enable sharing, a privileged provider user is excluded from those policies. Recipients, in turn, can define their own independent policies on their end. Provider and recipient policies are each enforced on their respective sides—there is no policy propagation between them—giving recipients the freedom to implement the access controls that are relevant for their organizations.
Step-by-Step: How ABAC Table Sharing Works
1. Building Shares for Data Recipients
Data providers select the assets to share and build a data share via Delta Sharing. No need to duplicate tables or manually recreate policy logic for each recipient.
2. Recipient-Side Governance & Additional Controls
After the table is shared, recipients can apply their own ABAC policies on the shared tables. To do so, recipients must ensure that the governed tags required by those policies are also applied on their side—policies alone are not sufficient without the corresponding tags. With this launch, recipient-side policies are now correctly enforced at query time. This lets recipients comply with their local governance requirements and implement additional business logic independently.
3. Policy Enforcement at Query and Share Time
When a recipient accesses shared data, recipient-side ABAC row filtering and column masking policies are evaluated based on the governed tags applied on their side, ensuring each user only sees the data they are authorized to view.
4. Auditing, Governance Log, and Compliance
Every action, every policy creation, sharing, access request, is logged in Unity Catalog. This traceability supports regulatory requirements, internal reviews, and audit trails necessary for enterprise organizations, and helps identify compliance concerns quickly.
Watch this short demo to see how data providers can easily share tables secured by ABAC policies, enabling recipients to govern and analyze the data while maintaining the provider's security and compliance requirements.
This seamless, governed approach to data sharing has already begun driving real-world impact for our customers. For instance, Yanolja, a global travel platform, has leveraged ABAC Sharing to improve their partner engagement.
At Noluniverse, we are constantly looking for ways to reduce the friction of data sharing across our various workspaces. With ABAC Sharing, the ability to apply dynamic policies via tags allows us to share data across multiple regions with total confidence. It ensures consistency and usability for all our data consumers without compromising on control. — Jaeseong Hwang, Data Engineering Team Lead, Noluniverse
Get started
- Watch this video to learn Delta Sharing best practices and real-world use cases.
- Read the Delta Sharing documentation to start sharing tables with ABAC policies.
Get the latest posts in your inbox
Subscribe to our blog and get the latest posts delivered to your inbox.