Solution Accelerator
Incident Investigation Using Graphistry
Pre-built code, sample data and step-by-step instructions ready to go in a Databricks Notebook

Investigate and analyze threat activities using your own language
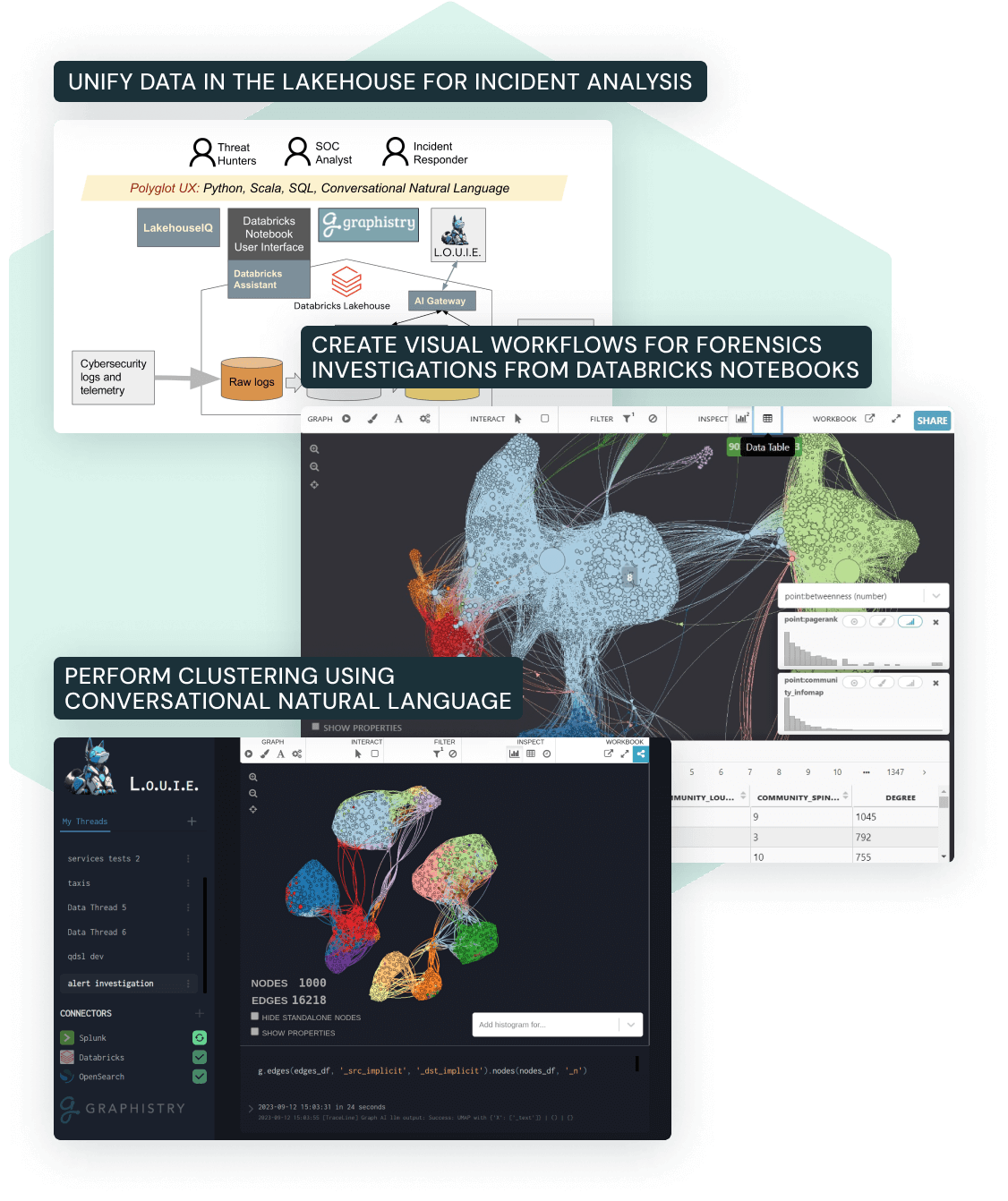
Sifting through vast amounts of log and telemetry data is key to investigating cybersecurity incidents. The ability to understand the patterns and relationships in the data is critical to uncovering the tactics, techniques and procedures used by the threat actor. This Solution Accelerator covers the following topics:
- Query for patterns or relationships in your investigation workflow using SQL, Python or Scala in Databricks Notebooks. Experience how the Databricks Assistant can help you write and debug your queries.
- Leverage graph analytics to visualize intricate connections and anomalies with Graphistry on the Lakehouse.
- Use conversational natural language to perform the investigative analysis via LakehouseIQ and L.O.U.I.E. Using the AI Gateway, you can easily switch between third-party LLM models (e.g., OpenAI) and a self-hosted LLM model that you developed in-house.